- DHCP Snooping
- Prevents DHCP server spoofing and exhaustion attack.
- Enforces DHCP server role on ports.
- Only trusted ports may respond to DHCP Discovers.
- ie. Trusted ports are connected to DHCP server.
- Only trusted ports may respond to DHCP Discovers.
- Maintains IP, MAC, and port binding.
- Could be used for security enforcement.
- Three main commands
- ‘ip dhcp snooping’
- ‘ip dhcp snooping VLAN x’
- ‘ip dhcp snooping trust <interface>’
- Caveats
- Don’t forget to trust port to server.
- Trust trunks as well as access port to DHCP.
- DHCP snooping inserts information option
- Adds empty giaddr field which IOS rejects.
- Information option insertion could be disabled.
- ‘no ip dhcp snooping information-option’
- Alternative is configure server to trust empty giaddr.
- Don’t forget to trust port to server.
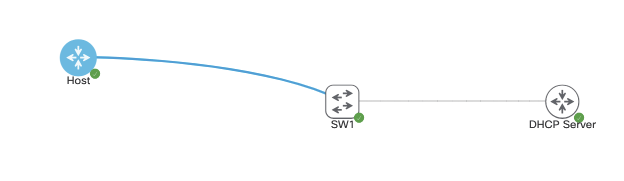
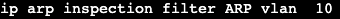
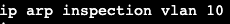
In the image above we have a host, switch and DHCP server. DHCP server is handing out addresses in the network 10.30.1.0/24 for VLAN 10, which our host is sitting in acting as a DHCP client. With DHCP snooping on, the configuration for our switch is as follows:

In global config we’re enabling DHCP snooping in vlan 10 and removing option 82 from the scenario. In addition we’re setting Gig0/1 as our trusted port that can receive DHCP requests.
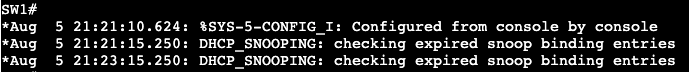
When I shut/no shut the host interface, the host tries to get another IP address from our server and on the switch we see it’s checking it’s snoop binding entries to make sure this is okay.
Dynamic ARP Inspection (DAI)
- Prevents ARP poisoning attack.
- Inspects ARP requests/responses
- ‘ip arp inspection VLAN X’
- ‘ip arp inspection trust (port command)’
- Enforces IP to MAC bindings based on DHCP snooping database
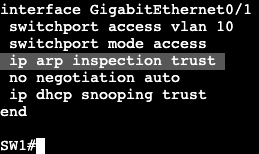
In global config we add arp inspection for VLAN 10 and allow our DHCP Server connecting interface to be trusted. Then we go into our host and manually change the MAC address of our interface and try pinging from our host to the DHCP server. In the switch we’ll see messages similar to this:
And of course the ping fails.
- IP Source Guard
- Prevents IP address spoofing
- Uses DHCP snooping database to filter IPs on the port dynamically.
- ‘ip verify source’ – interface command
- MAC address filtering could be enforced as well.
- Requires port-security enabled on interface.
- Additional parameter ip verify source port-security.
- Static IP to MAC mapping on a VLAN.
- ‘ip source binding’ – global config command.
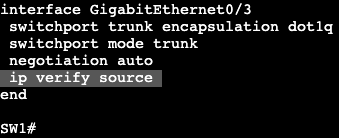
Notice it’s an interface level command on our untrusted port.
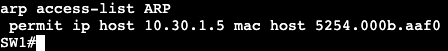
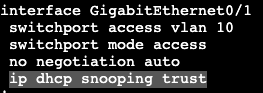
Dynamic ARP inspection WITHOUT DHCP:
- If DHCP is not used static ARP mappings can be configured.
- Takes precedence over dynamic ARP entries.
- Configured using ARP inspection ACL.
- ‘arp access-list x’
- ‘permit ip host <ip> mac host <mac-address>
- Applied to a VLAN
- ‘ip arp inspection filter <NAME> VLAN y