- Used to leak traffic from VRF table to global table.
- Requires static routing with next hop and global keyword
- ‘ip route VRF1 0.0.0.0 0.0.0.0 gig0/1 1.2.3.4 global
- NAT statement is VRF aware.
- ip nat inside source list 1 interface gig0/1 vrf VRF1 overload

The topology above shows a host on the internal RFC 1918 network 192.168.10.0/24. R6 will be doing some NAT functions to the ‘Internet’. R6 has private IP on the link to host, and public on the link to R4.
First configuration will be creating a new VRF and adding interface gig0/0.10 into it, which is the interface connecting to ‘Host’.
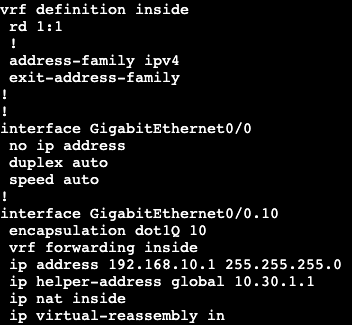
After adding the interface into the VRF we need to re-add the IP information like always.
This will cut off connectivity to the rest of the network because all of the routing is in R6’s global routing table, not the routing table associated with VRF ‘inside’.
To fix this we need to create a default route in the VRF to our next hop upstream, but specify the next hop is the global routing table. In addition, we’ll need to NAT traffic from the VRF to the outside interface. We’re going to do this with via an overload NAT/PAT.


The default route here has a next hop of R4 and we’re pointing from the VRF to the global routing table.

And then we’re creating an overload NAT statement that references our VRF ‘inside’.
Now from our host we can reach past just our gateway/VRF on R6.