IPSEC with IKEv1 configuration is going to leverage the topology/lab that’s already setup with plain DMVPN mGRE.

The configuration is already setup with BGP and R5 as the hub. The below configuration will be the same on every router and it will add IPSEC encryption over each tunnel.
crypto isakmp policy 1
encr aes
authentication pre-share
group 14
crypto isakmp key Cisco47 address 0.0.0.0
crypto ipsec transform-set trans2 esp-aes esp-sha-hmac
mode transport
crypto ipsec profile vpnprof
set transform-set trans2
int tunnel 0
tunnel protection ipsec profile vpnprof
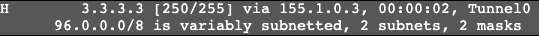
Now on R1 we’re going to ping R3 and form the direct tunnel. On R1 we now see an ‘H’ route and the direct tunnel under ‘show dmvpn’.

The difference though between now and normal GRE, a ‘show crypto ipsec association’ shows a direct IPSEC tunnel between R1 and R3.
