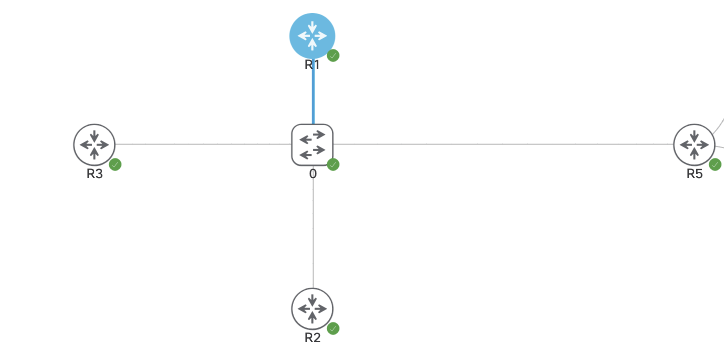
The below topology is running DMVPN Phase 3. R1-3 are spokes and R5 is the hub. Currently the routers are all running IPSEC via IKEv1 and we’re going to change this to IKEv2.
- IKEv1 vs. IKEv2 (out of scope for CCIE)
- IKEv2 can use asymmetric authentication.
- ie. one side running PSK and other running PKI.
- IKEv1 has to be the same on both.
- IKEv2 can use asymmetric authentication.
By removing the line ‘no tunnel protection ipsec profile vpnprof‘ we’re able to remove IPSEC IKEv1 from each tunnel interface. The IKEv1 configuration will still be on the box but not applied to anything.
The configuration for IKEv2 will be the following:
crypto ipsec transform-set cisco-ts esp-aes esp-sha256-hmac
mode transport
crypto ikev2 keyring cisco-ikev2-keyring
peer dmvpn-node
description symmetric pre-shared key for the hub/spoke
address 0.0.0.0 0.0.0.0
pre-shared-key cisco123
crypto ikev2 profile cisco-ikev2-profile
match identity remote any
authentication remote pre-share
authentication local pre-share
keyring local cisco-ikev2-keyring
authentication local pre-share
match address local 0.0.0.0
crypto ipsec profile cisco-ipsec-ikev2
set transform-set cisco-ts
set ikev2-profile cisco-ikev2-profile
int tunnel 0
tunnel protection ipsec profile cisco-ipsec-ikev2
NOTE – Transport vs. Tunnel mode:
- Transport
- Encrypts only the payload of packets, not the header.
- Tunnel
- Encrypts the entire payload and header.
- Ultimately more secure.
After these lines are configured on ALL routers, the VPN tunnels and BGP adjacencies move into the Up state.