- HSRP
- Cisco Proprietary
- Elects active by priority.
- Default 100, max 255
- Highest IP as Tie-Breaker
- No preempt by default.
- Highest priority wins
- Uses UDP 224.0.0.2 port 1985
- Can use authentication by MD5 or cleartext
- Supports multiple groups per interface
- Group ID encoded in Virtual MAC.
- VRRP
- Standards based alternative
- RFC 3768
- Uses terms master/backup as opposed to active/standby
- Other concepts are similar
- Uses transport protocol 112 and 224.0.0.18
- Virtual MAC is 0000.5e00.01xx
- Preemptive by default.
- GLBP
- Cisco Proprietary
- Extends HSRP functionality to support load balancing.
- Transport via UDP 3222 and 224.0.0.102
- Every physical gateway can be active.
- Called active virtual forwards (AVF)
- Each AVF is assigned virtual MAC.
- One gateway responds to ARP requests for GLBP IP
- Called Active Virtual Gateway (AVG)
- ARP response uses virtual MACs of AVFs to implement load-balancing.
- LOAD BALANCING IS COMPLETED BY CLIENT, NOT FLOW.
- AVG
- Elected based on priority
- By default only AVF, all others standby.
- No AVG preemption by default.
- Enable using glbp preempt
- To enable load balancing:
- ‘glbp xxx load-balancing weighted’
- Assign weights with ‘glbp xxx weighting Y’
- Weight can be adjusted based on object tracking.
- FHRP enhanced object tracking
- Gateway recovery relies on correct failure detection.
- eg. FHRP keepalives or BFD.
- What if southbound link is up but northbound is down?
- REsult is Active/master maintains bizz as usual.
- Solution:
- Setup IP SLA with FHRP.
- Object tracking is bound to priority.
- Decrement priority if object is down.
- Assumes preemption is configured.
- Gateway recovery relies on correct failure detection.
- IPv6 support
- HSRPv2
- Increases group range
- adds new dedicated transport add 224.0.0.102
- Doesn’t overlap with ALL ROUTERS
- Adds IPv6 support.
- Enabled with int level standby version 2
- VRRPv3
- RFC5798
- enabled with global ‘fhrp version vrrp v3’
- HSRPv2

HSRP Config:
From the topology above, we’re going to run HSRP between R6 and R4. This will provide redundancy for the host to internet if one of the gateway routers were to fail.
R6 and R7 are the gateways for the LAN network 10.30.1.0/24. The host is using a default gateway of 10.30.1.1 and R6/R7 will setup that VIP. To get HSRP running it only requires these commands on each box:

Note each physical interface has an IP in the lan – 10.30.1.2 and 10.30.1.3.
On the host now we can see the Virtual MAC address for 10.30.1.1 and on R6 we can see which router is the active node:

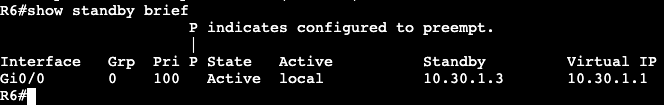
R6 is active and R4 is standby.
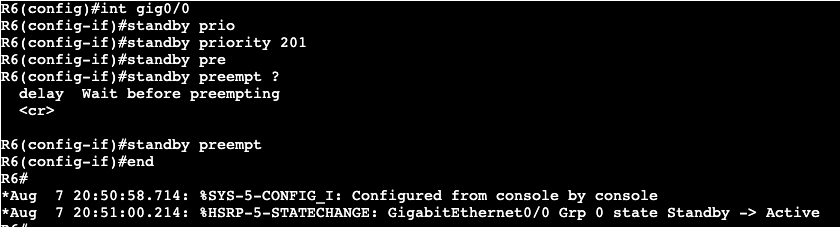
If we want to switch which router is active, we’ll add the priority command that is higher than the default 100, which is what R4 is currently using.

Pre-emption is not enabled, which means this will not take affect until the HSRP election comes up again.

After I shutdown the LAN interface on R6, R4 became the active router. Now if I change the priority of R6 to something higher than 200, then enable preemption, R6 will take over as active again.
Often times two devices running HSRP are doing this process for multiple gateways/VLANs/Subnets, and each process is running the multicast keepalives between the two routers. In order to minimize this chatter and CPU overhead, BFD can be used between the two boxes for ALL processes.
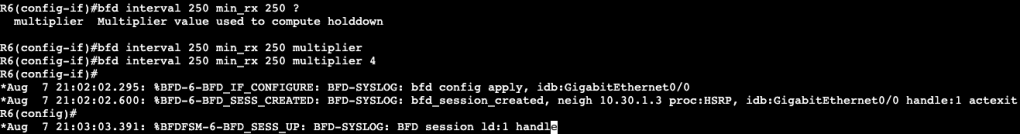
Under the interface on R6 we add the command ‘bfd interval 250 min_rx 250 multiplier 4’ and immediately BFD starts working with HSRP. The same command gets added to R4.


By default in IOS-XE, BFD is already enabled for HSRP if you turn it on under the interface that’s running HSRP.
Authentication:
- If we want to add authentication for an extra layer of security between HSRP nodes, the config is below.
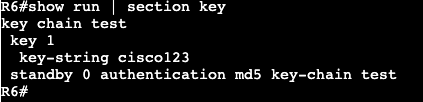
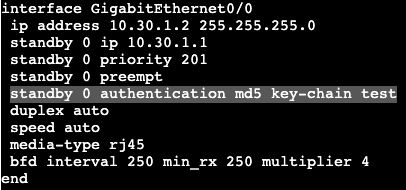
- For MD5 authentication we’ll first create a key chain in global config, then apply that keychain to the authentication string under the standby interface command.
Object Tracking:
In the topology, we have the ‘Internet’ host with a loopback of 8.8.8.8 that we’re going to use as an example of object tracking. R6 is going to run an ongoing ping to 8.8.8.8 and if it fails to reach the destination, it will be configured to leave the HSRP active state.

The IP SLA has been configured, but not applied to HSRP yet. This needs to be added under the interface running the VIP.

Decrement means that if the IP SLA tracking fails, decrement the router priority by 101. The priority would then be 100, lower than R4’s 200.
The last step is configuring the tracking object. The tracking object configuration is below:

Below is what happens when the loopback interface on ‘Internet’ goes down.
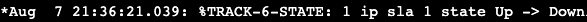
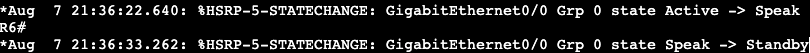

R4 took over as active HSRP and the Standby router priority is now 100 instead of 201.