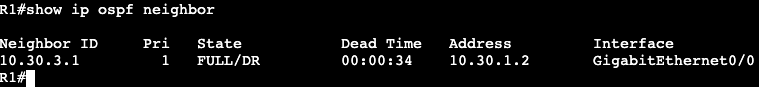
- OSPF has multiple network types that need to be compatible in order to form OSPF adjacencies.
- Most common in Enterprise are Point-to-Point and Broadcast/Multiaccess.
- When troubleshooting an OSPF adjacency issue, check on both ends that the interface network types are setup the same.
- Default is broadcast/multiaccess
- Will include DR/BDR election
- Point-to-Point
- Expects there to be a single adjacency/single OSPF speaking node.
- Point-to-Multipoint
- Needed on specific hub and spoke network types, like DMVPN.
- The Hub will need this command to form adjacencies with multiple spokes. Each spoke will be configured as point-to-point.
- Default is broadcast/multiaccess
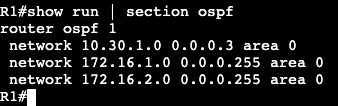
Configuration of network types is done on the interface level.
- Normal Broadcast/Multiaccess:
- No specification in config, default.
- ‘show ip ospf neigh’ will show a DR/BDR/DROTHER relationship.

- Point-To-Point:
- ‘R5(config-if)#ip ospf network point-to-point’
- ‘show ip ospf neigh’ will show a Full adjacency without the DR/BDR/DR
- Point-To-Multipoint
- ‘R5(config-if)#ip ospf network point-to-multipoint’
- Point to Multipoint will change the OSPF timers on the interface to something that’s different than the default for Broadcast/Multiaccess and Point-to-point.
- If using point-to-multipoint with Broadcast/Multiaccess or point-to-point, the hello timers will need to be changed on one of the sides to match.
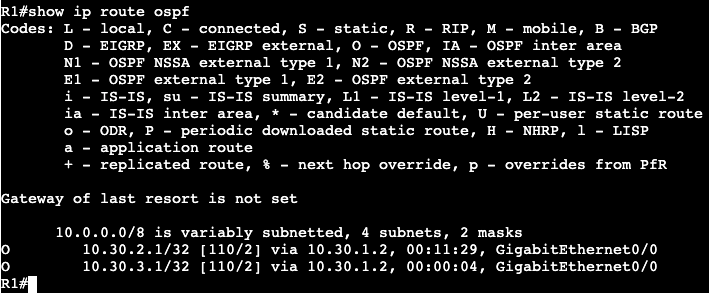
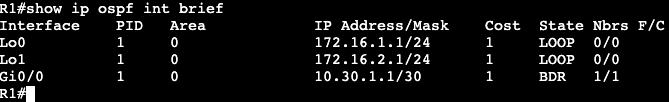
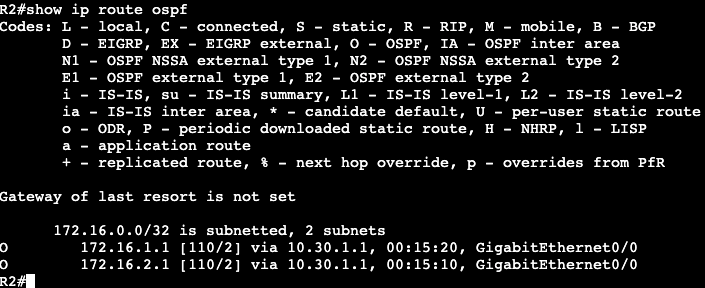
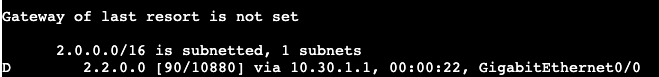
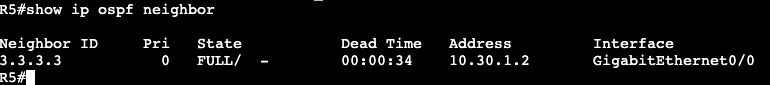
The image below shows two routers running OSPF. R5 is operating in point-to-multipoint, and R3 is running in normal broadcast.
Running a ‘show ip ospf int gig0/0’ shows that R5’s interface is running in point-to-multipoint and it’s timers are 30, 120, 120.
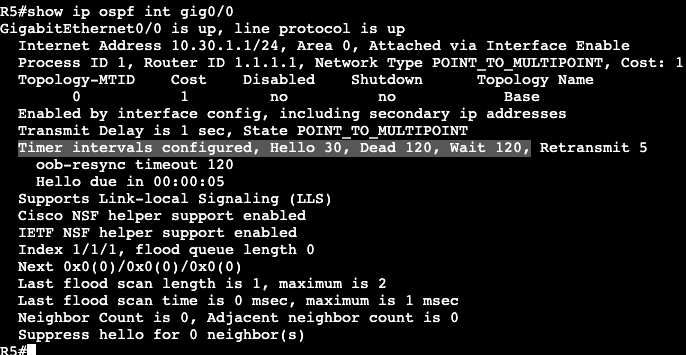
The router R5 is trying to form an adjacency with is running in normal broadcast mode, which sets the Hello timer to 10, 40, 40.
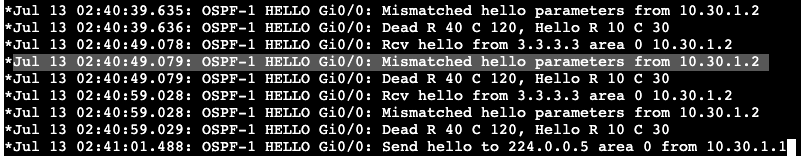
Adding a ‘debug ip ospf hello’ and bouncing R5’s interface shows the problem as well. What needs to be configured are the hello timers on R5 or R3 to match. On R3 the below command was added and the adjacency came up between broadcast and point-to-multipoint networks.
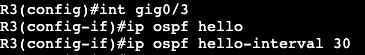

Above we can see the intervals were changed on R3’s interface, and below the adjacency shows with a much higher dead time than the default 10 seconds in a broadcast or point-to-point network.

This example in general is a bit odd because it’s forming an adjacency between a Broadcast network and a point-to-multipoint. It doesn’t appear as if it should actually be working. When I changed the hello interval to match on both sides, the adjacency came up. When I tried exchanging routes I could not get it to work. Then I took the adjacency down and could not get it to form again until I set the broadcast to point-to-point. Routes began exchanging between both nodes as well. In general the timers change is still valid though. The hello interval would have had to be changed if I was working with a point-to-point network type the entire time.
Correction – The Point-to-Multipoint and Broadcast network types are not compatible. Compatibility depends on whether the LSA Type 2 (DR/BDR) is being used. Type 2 is used in broadcast and not in Point-to-Multipoint.